What ISO 31000 actually requires
ISO 31000:2018 is a principles-based standard. It does not mandate specific tools, templates, or registers. What it does require is that risk management is integrated into organisational processes, not run as a parallel activity that reports to the board annually and informs nothing in between.
The standard requires that risks are identified from real context, assessed against specific criteria, treated through deliberate decisions, and monitored as conditions change. The output should be defensible — meaning a risk assessment can be traced back to the evidence that produced it.
Most organisations satisfy the form of ISO 31000 without the substance. A risk register exists. It was updated last quarter. It does not connect to the architecture decisions made this month, the vendor assessment that flagged a new threat, or the project portfolio absorbing change capacity.
The gap most organisations fall into
Risk management and IT strategy are produced by different teams, in different cycles, on different templates. The board sees a risk register in one paper and a technology roadmap in another — and no one has checked whether the risks on the register are reflected in the sequencing of the roadmap.
Disconnected documents
Audit findings sit in a PDF. The risk register was last updated when the audit was tabled. Neither feeds the technology roadmap.
Annual, not continuous
ISO 31000 requires ongoing monitoring. Most organisations do this once a year, which means the risk picture is always ten months out of date.
No traceability
When the board asks why a risk is rated High, the answer is 'because the consultant said so.' The source evidence is gone.
Treatment not tracked
Risk treatments are listed in the register but not connected to the projects responsible for closing them. Treatment status is unknown.
How Kogira implements ISO 31000
Kogira is not a risk register tool. It is an IT strategy platform that derives risks from evidence — meaning every risk on the Kogira risk register has a source, and that source is a specific paragraph in a specific document your organisation uploaded.
Evidence-linked risk identification
Kogira reads your uploaded documents — board papers, audit reports, vendor assessments, operational reviews, risk policies — and extracts risk signals. Each identified risk traces to the source paragraph. When the board asks why a risk is on the register, you show them the sentence that surfaced it.
5×5 impact-probability assessment
Risks are scored on a standardised 5×5 matrix: impact (1–5) and probability (1–5). The combined score drives priority — Critical, High, Medium, Low. Scores are set from evidence context, not gut feel, and can be adjusted with documented rationale.
Treatment planning connected to strategy
Each risk links to a treatment recommendation. Treatments are not standalone items — they connect to the technology roadmap. When a project closes a risk treatment, Kogira marks it as addressed. The risk register stays current without manual updates.
Cross-framework integration
ISO 31000 risks feed into the TOGAF architecture assessment and the CMMI maturity gap analysis. A risk flagged in the risk register that relates to an architecture capability gap surfaces in both views. The board paper draws from one integrated evidence base, not three separate reports.
The risk dashboard
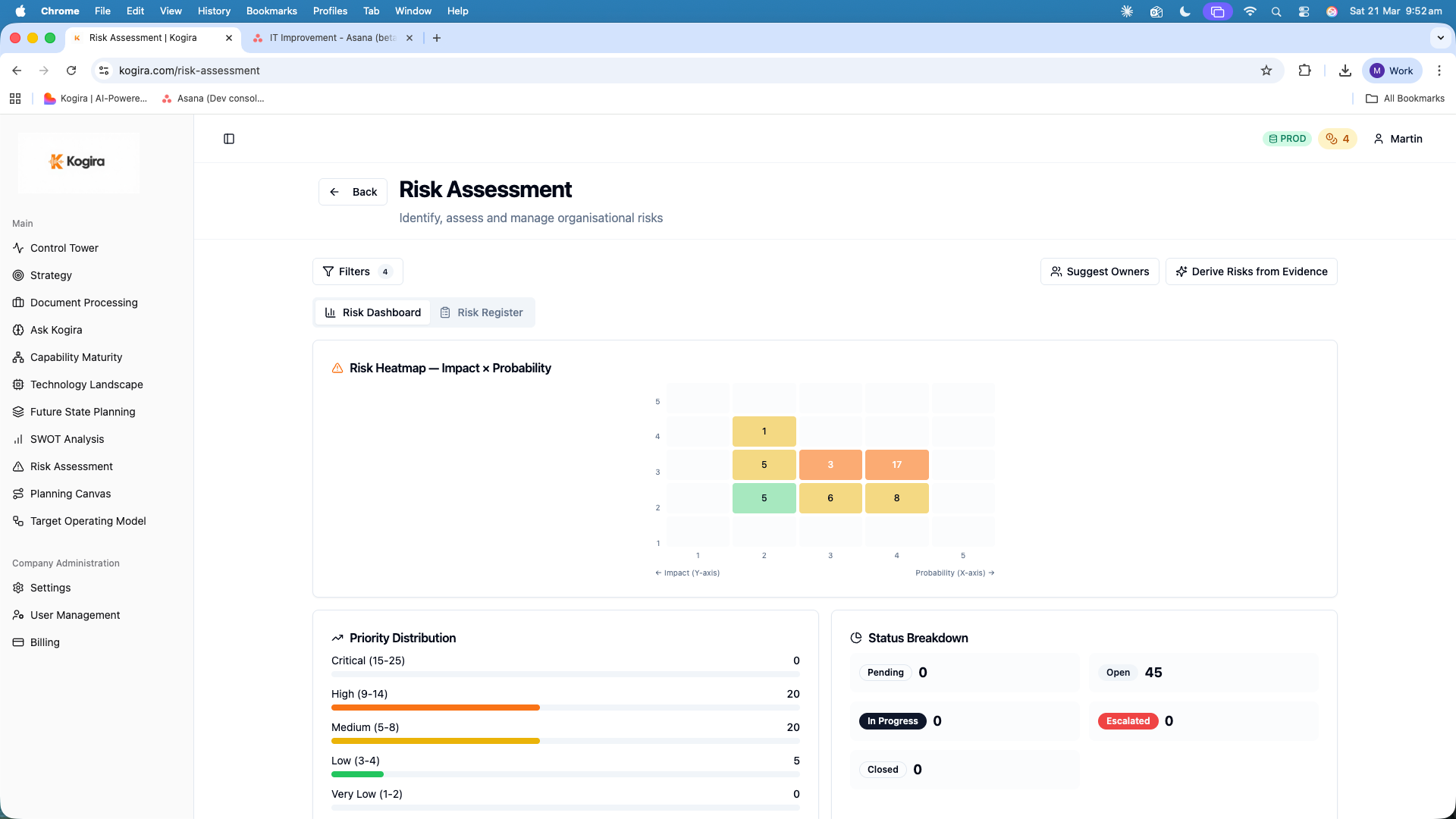
Risk register with impact-probability heatmap, evidence linkage, and treatment tracking.
Common questions
Does Kogira comply with ISO 31000:2018?
Kogira's risk module is built to align with ISO 31000:2018 principles. Risk identification draws from uploaded documents via evidence extraction. Each risk is assessed on a 5×5 impact-probability matrix. Treatment plans are tracked and linked to strategic objectives. Every risk traces to the source paragraph that surfaced it.
How does Kogira identify IT risks from documents?
Kogira reads uploaded documents — board papers, audit reports, vendor assessments, operational reviews — and extracts risk signals using structured evidence extraction. Identified risks are classified by category, scored on impact and probability, and mapped to the relevant IT domains they affect.
What is the difference between a risk register and ISO 31000 risk management?
A risk register is a list. ISO 31000 risk management is a continuous process: identify, assess, treat, monitor, and communicate. Most organisations have risk registers that are updated annually and disconnected from strategic decisions. Kogira connects risk identification to evidence, risk treatment to strategy, and risk monitoring to delivery progress.
Can I use Kogira's risk module alongside my existing risk framework?
Yes. Kogira generates ISO 31000-aligned outputs that can supplement or feed into broader enterprise risk management processes. The risk register export and evidence linkage make it easy to bring Kogira's findings into board reporting or existing GRC tools.
How does Kogira's risk management connect to TOGAF and CMMI?
Kogira treats TOGAF, CMMI, PMI, and ISO 31000 as an integrated model, not separate frameworks. Architecture decisions from TOGAF are risk-informed. CMMI maturity gaps surface as risk inputs. PMI program governance gates include risk treatment requirements. All four frameworks share the same underlying evidence base.